
The lure of a £250 voucher from Aldi is the carrot used to hook the big phish today. Indeed, some of you may have already received this one. I got my “invite” twice on WhatsApp already.
The post wants you to visit the site:
http:[//]www[.]aldi[.]co[.]uk-market[.]club
I spotted the problem straight away. The first issue is the http. Aldi simply wouldn’t use http. All their sites are https.
I also spotted the “uk-market” part. This is a nice slight of hand to fool the user into trusting the initial scam.
I threw this url straight into Virustotal and this came up clean. I also threw it into urlscan.io, which is an excellent sandbox. This is where it gets interesting.
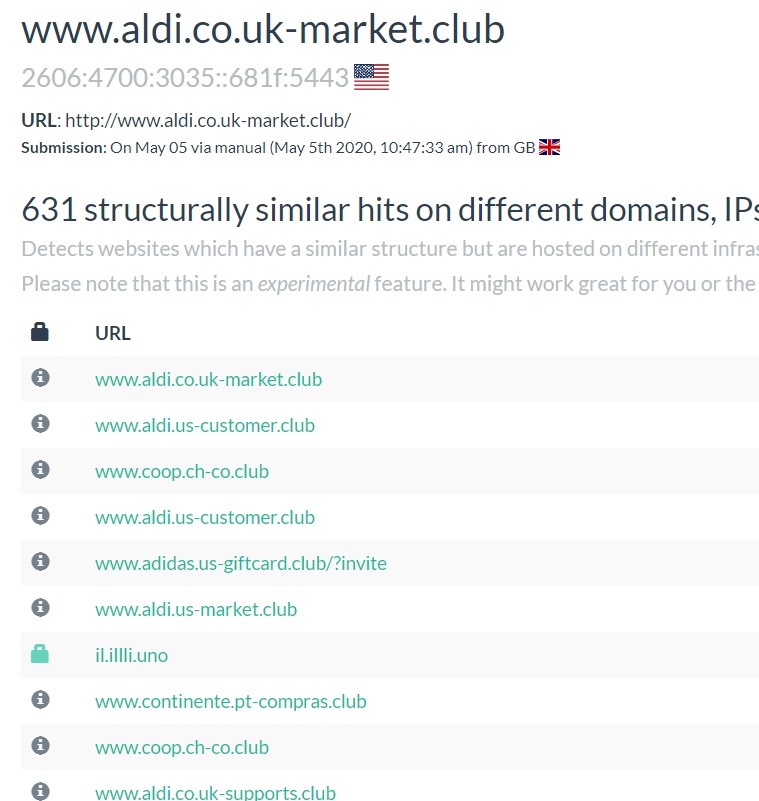
I was the first to scan this site, but it’s got a neat feature that allows you to spot similar domains and site structures. This shows the spread of this scam.
The page relies upon images uploaded into imgur, which is a red flag as well.
You can see from the screen shot on the left, there are many, many similar scams going on and most have emerged today. So this is a big new phishing campaign which is pulling on the coat-tails of Aldi and COVID-19.
Digging into the domain itself. It looks like this is a cloudflare fronted set of domains.
Using urlscan.io it’s possible to view the HTML DOM and scripts that the site loads.
The key script is called “voucherf0c9.js”. Doing a search for this on urlscan.io allow insight into the vast number of scams that use this script and also the evolution of the hosting.
It looks like the scam originally targeted Marks and Spencer, Costco, Trader Joes, Adidas, Home Depot and currently Aldi.
Take Home Tasks
There is a take home here, which is never click on an unsolicited link. Only click if you were expecting the link and you can be sure that the link is trustworthy. Check the raw url, trustworthy sites will use HTTPS. If in doubt use a trustworthy validation site, like Virustotal and urlscan.io. Even better, if you have a concern, delete the link.

Leave a comment