Hello, cyber fans! Welcome to the first episode of Popcorn and Cyber, where we watch and discuss movies that feature hacking and cybersecurity. Today, we are going to talk about one of the most iconic and influential sci-fi movies of all time: The Matrix.
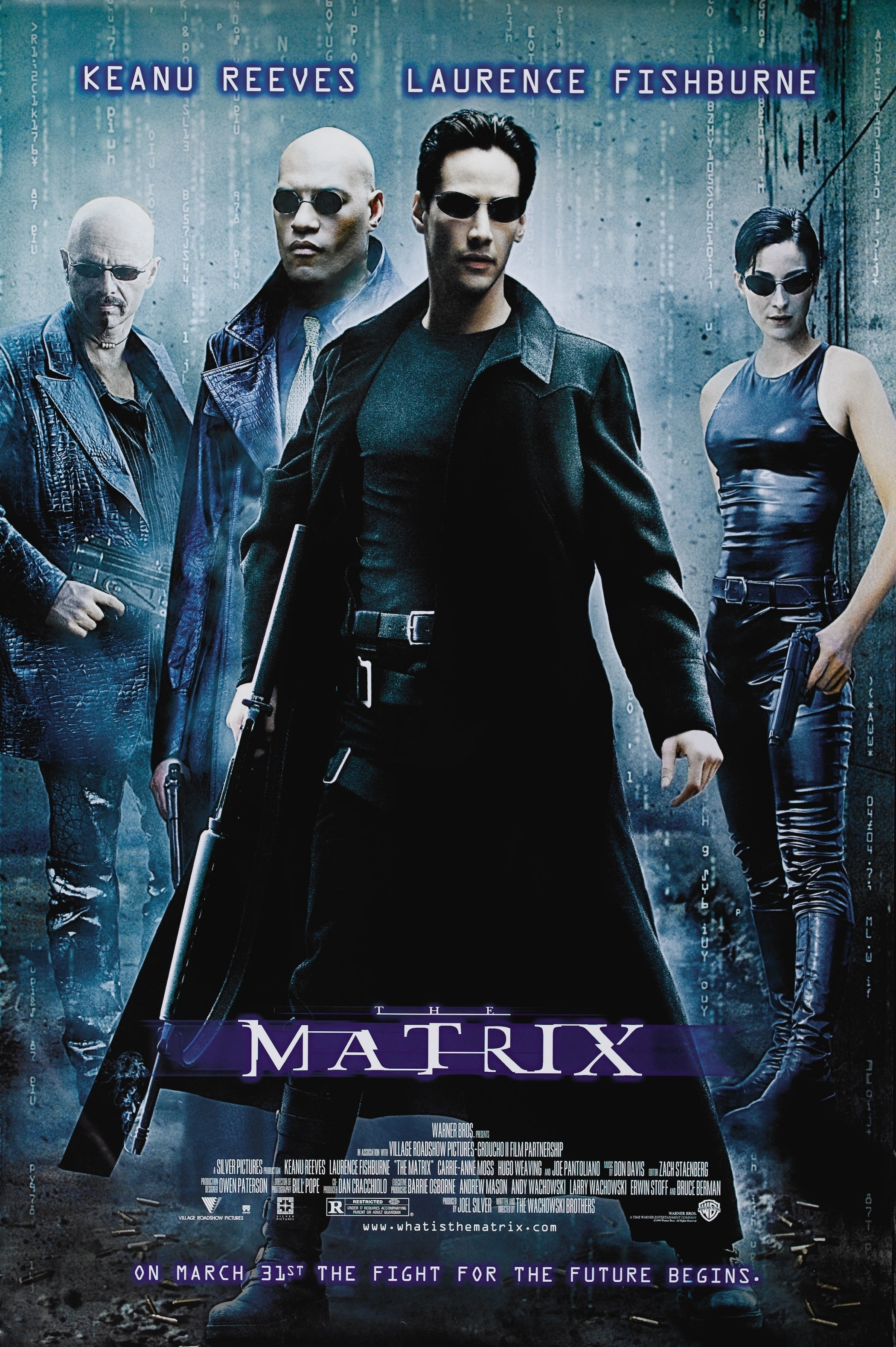
The Matrix is a 1999 film written and directed by the Wachowskis, starring Keanu Reeves as Neo, a computer hacker who discovers that the world he lives in is a simulated reality created by intelligent machines to enslave humanity. He joins a group of rebels led by Morpheus (Laurence Fishburne) and Trinity (Carrie-Anne Moss) who fight against the machines using their knowledge of the Matrix and their martial arts skills.

The Matrix is widely praised for its innovative visual effects, action sequences, cinematography and entertainment value. It won four Academy Awards for Best Visual Effects, Best Film Editing, Best Sound and Best Sound Editing. It also popularized a technique called “bullet time”, which allows the action to slow down while the camera moves around the scene, creating a stunning effect of frozen time.
But how realistic is The Matrix when it comes to hacking and cybersecurity? Well, let’s find out.
First of all, let’s talk about the premise of the movie. The idea that machines could create a virtual world to harvest human energy is not very plausible, for several reasons. One is that human bodies are not very efficient sources of energy, compared to other alternatives like solar power or nuclear fusion. Another is that machines would have to maintain a complex infrastructure to keep humans alive and connected to the Matrix, which would consume more energy than they would produce. And finally, why would machines bother to create such a detailed simulation of human history and culture, instead of just keeping humans in a coma-like state?
A more realistic scenario would be that machines use humans as a source of information or computation, rather than energy. For example, they could use human brains as nodes in a distributed network, or exploit human creativity and intelligence for their own purposes. This would also explain why some humans can manipulate the Matrix with their minds, as they are actually accessing the underlying code of the simulation.
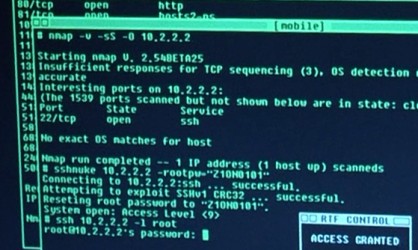
Secondly, let’s talk about the hacking techniques used by the rebels. The movie shows them using various devices and programs to hack into the Matrix, such as phones, laptops, disks and sunglasses. Some of these are based on real-world technologies, such as encryption, viruses and backdoors. However, some of them are also exaggerated or fictionalized for dramatic effect.
For instance, the movie depicts hacking as a fast and easy process that can be done with a few keystrokes or voice commands. In reality, hacking is a complex and time-consuming activity that requires a lot of skill, knowledge and patience. It also involves a lot of trial and error, research and analysis, rather than just guessing passwords or finding loopholes.
Another example is the use of phones as portals to enter and exit the Matrix. The movie implies that any phone can be used for this purpose, as long as it is connected to a hard line. However, this raises some questions: How do the rebels know which phones are safe to use? How do they avoid detection by the machines? How do they transport their equipment from one location to another? And why do they need phones at all, if they can hack into the Matrix directly?
A more realistic explanation would be that phones are not actually portals, but rather devices that allow the rebels to communicate with their ship outside the Matrix. The actual portals are hidden in specific locations that only the rebels know about, such as subway stations or abandoned buildings. The phones are also encrypted and disguised as normal calls, to avoid attracting attention from the machines.
Thirdly, let’s talk about the cybersecurity measures taken by the machines. The movie shows that the machines have agents who patrol the Matrix and hunt down any anomalies or threats. These agents are superhuman programs who can take over any human body within the simulation. They can also bend or break the rules of physics within the Matrix, such as dodging bullets or jumping from building to building.
However, these agents are not very effective at stopping the rebels. They are often outsmarted or outmatched by them in combat. They also seem to have limited resources and intelligence, as they rely on human informants or outdated information to track down their targets.
A more realistic approach would be that the machines would have more sophisticated and diverse cybersecurity measures to protect the Matrix and their own systems. For example, they could use encryption, firewalls, intrusion detection and prevention systems, honeypots, malware analysis, threat intelligence, incident response, recovery plans, etc. They could also employ more advanced artificial intelligence and machine learning techniques to analyze and predict the behavior of the rebels and adapt their strategies accordingly. They could also leverage their control over the simulation to create more realistic and convincing scenarios to deceive or manipulate the rebels.
Of course, these are just some of the possible ways that the Machines could improve their cybersecurity posture. However, we also have to remember that the movie is not meant to be a realistic depiction of hacking and cybersecurity, but rather a metaphor for questioning reality and challenging authority. The Matrix is a story about human freedom, choice, and destiny, not about technical accuracy or feasibility.

Therefore, we should not judge the movie too harshly for its unrealistic aspects but rather appreciate it for its artistic vision and cultural impact. The Matrix is a movie that inspired many people to learn more about hacking and cybersecurity, as well as philosophy, religion, and mythology. It also influenced many other movies, games, books, and comics that explore similar themes and concepts.
The Matrix is a movie that deserves to be watched and rewatched by cyber fans and non-cyber fans alike. It is a movie that makes us think and feel, as well as entertains us with its spectacular action scenes and visual effects. It is a movie that has become a part of our collective imagination and culture.
So grab your popcorn and cyber gear, and join us next time for another episode of Popcorn and Cyber, where we will discuss another cyber-related movie. Until then, remember: there is no spoon.

Leave a comment